Role: Staff UX Designer
Timeline: 3 weeks
Team: PM + Security Analysts + Engineering
Impact
- 40% faster breach investigation
- 60% fewer navigation steps
- Unified investigation dashboard
Problem Context
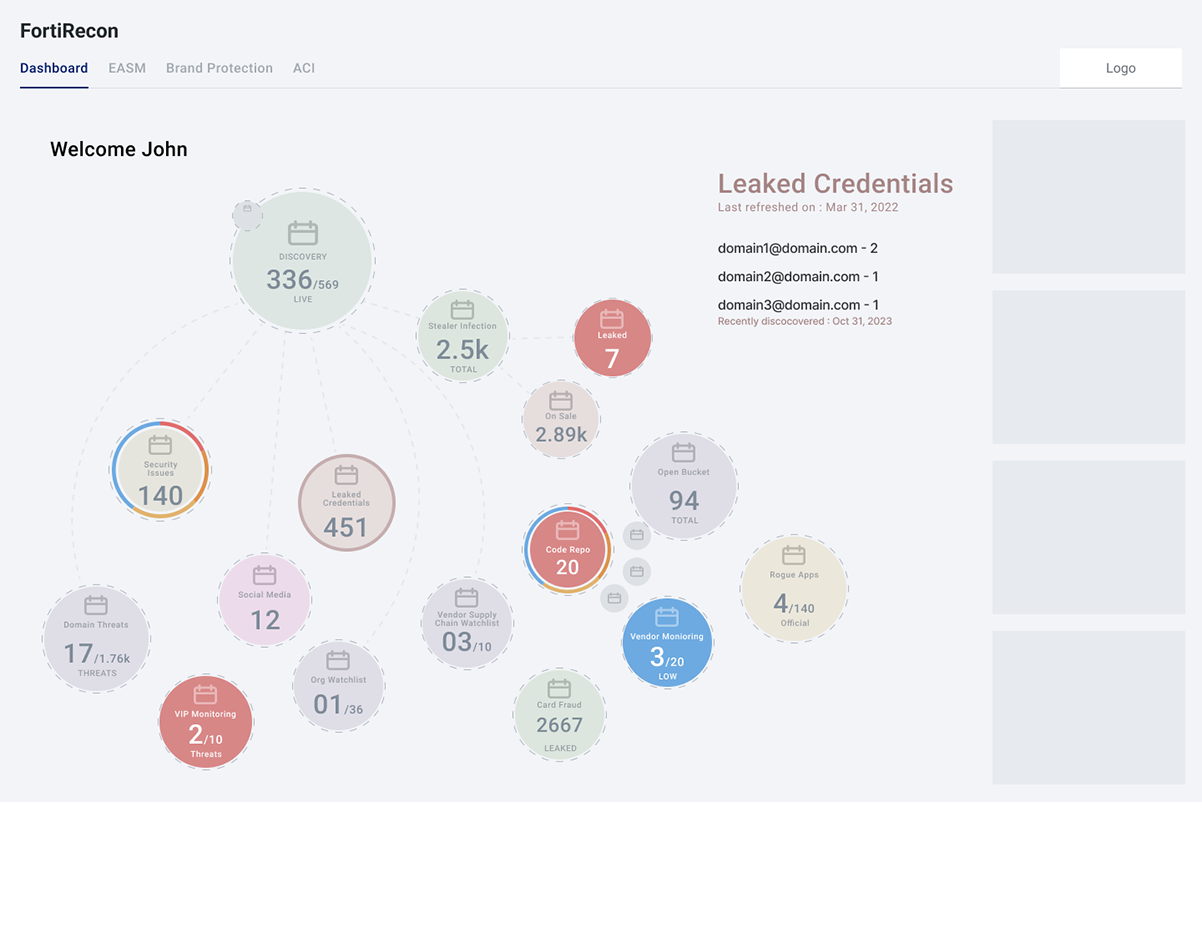
- Organizations monitor thousands of digital assets such as domains, credentials, IP addresses, and social media accounts to detect potential breaches.
- FortiRecon aggregates this intelligence, but security analysts must navigate multiple modules to investigate a single breach incident.
- This fragmented workflow makes breach investigation slow and cognitively demanding.
Current Investigation Workflow

Too many disconnected systems, No unified breach investigation view
My Design Thinking Process
User Research
To understand analyst workflows, I conducted interviews with security professionals using FortiRecon.

User interview results >
UX Problem Statement
This is the core design challenge.

Design Goals
To address the fragmented investigation workflow identified during user research, the redesign focused on three primary goals.
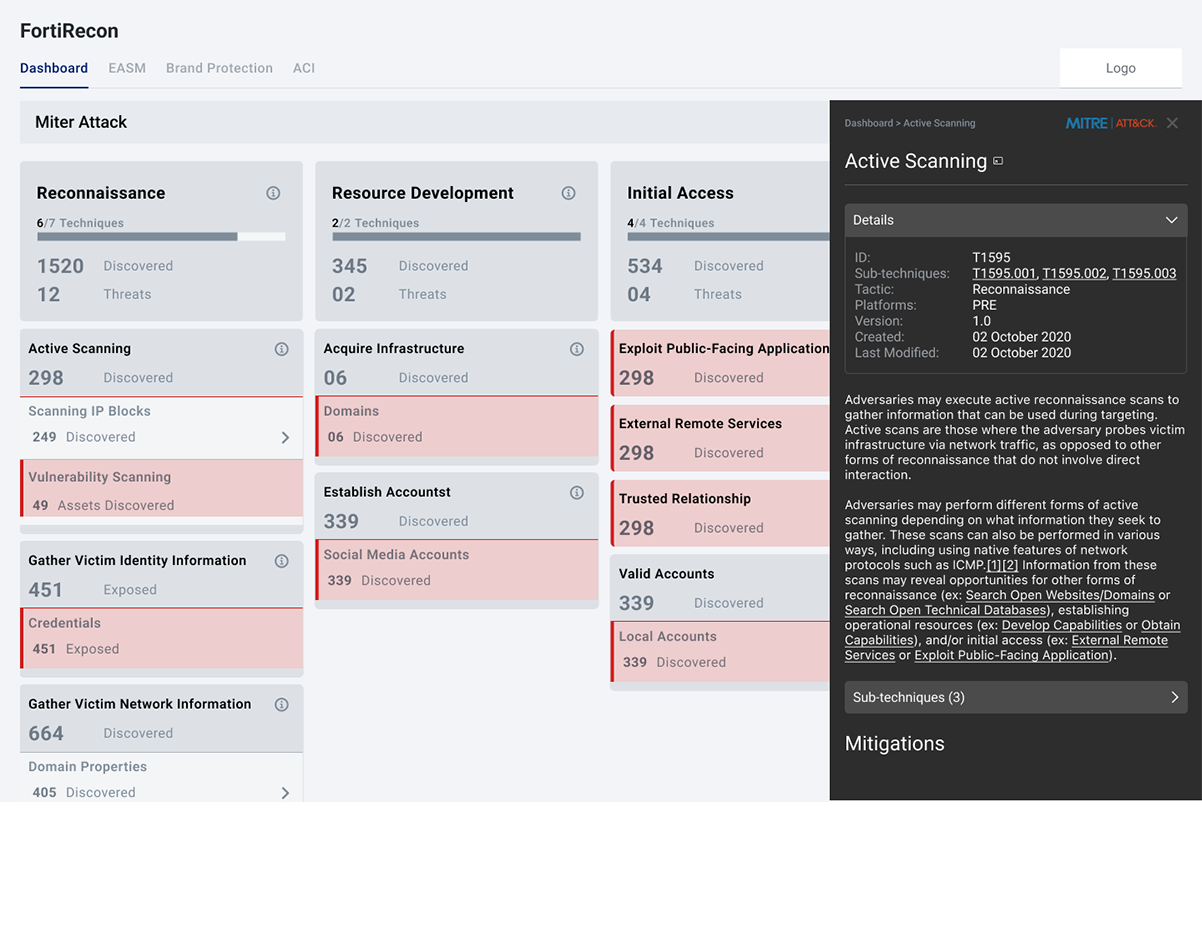
Goal 1 — Create a Single Investigation View
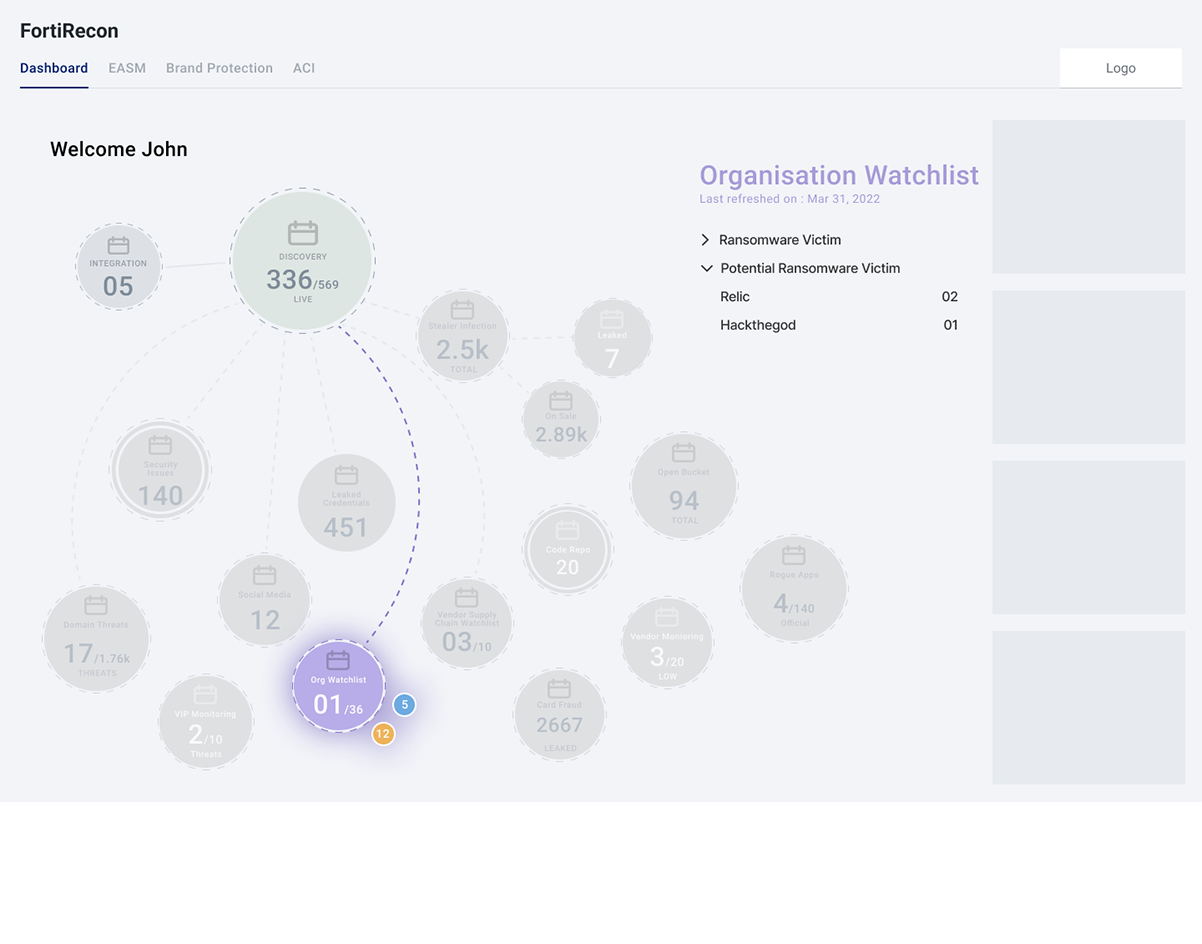
Security analysts currently navigate multiple modules (domain monitoring, credential leaks, social monitoring, threat feeds) to investigate a potential breach.
The goal was to consolidate these signals into a single investigation workspace where analysts can view alerts, correlated signals, and impacted assets without switching between different modules.
Goal 2 — Reduce Navigation Across Modules
Frequent context switching between modules increases investigation time and cognitive load.
The redesign aims to minimize navigation steps by centralizing key information and enabling analysts to access related signals and investigation details within the same workflow.
Goal 3 — Help Analysts Understand Breach Context Quickly
Security analysts need to quickly determine whether a threat is real and understand how the attack evolved.
The design focuses on providing clear context through correlated signals and attack timelines, allowing analysts to understand the sequence of events and the potential impact more efficiently.
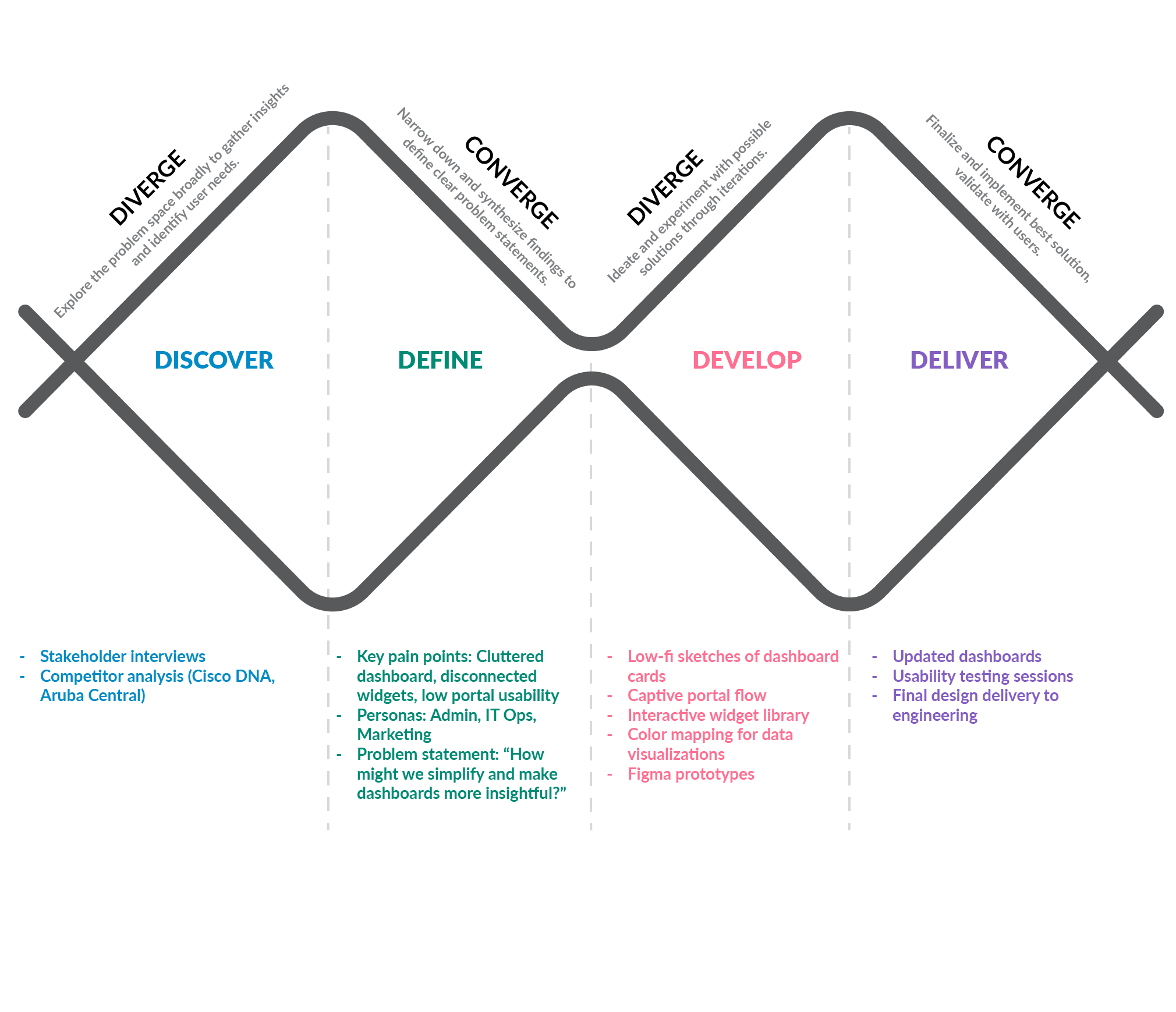
Design Timeline
I applied a Lean UX framework, focusing on three iterative milestones over a 4 weeks timeline. This approach emphasized swift, structured progress with a continuous feedback loop, ensuring agility and effective collaboration throughout the project.

Information Architecture
The information architecture organizes threat intelligence signals, investigation modules, and contextual intelligence into a unified investigation workspace.

Ideation(Persona)

Idea visualization
with the extensive feedback loops and we were involved in transforming our ideas into visual concepts" highlights a collaborative and iterative approach to bringing abstract ideas to life through visual representation.